As citizens of local municipalities, cities, and states we rely on local government agencies every day to ensure we have critical services such as water, sewers, transportation, schools, health service, and emergency services. And in an increasingly digital world government agencies are delivering faster, more effective services for citizens including California Child Support Services and Nevada Department of Transportation. As agencies embrace digital services, they’re also seeing increasing threats from bad actors using advancements in technology (bots and malware) to take advantage of public agencies, with zero disregard for those they hurt. Ransomware was up 25% in 2021 year accordingly to Verizon’s data breach investigations report 2022. The list of threats continues to rise, while State and Local Government leaders have more demands and less resources to combat the ever-growing security risks. There are several actions government IT admins can take to increase their organizational security resilience and continue to deliver the citizen services, including: building the right team to assess your current security environment and utilizing a comprehensive security portfolio to maximize protection and reduce data exposure.
Reinforce your security defenses with a data loss prevention plan.
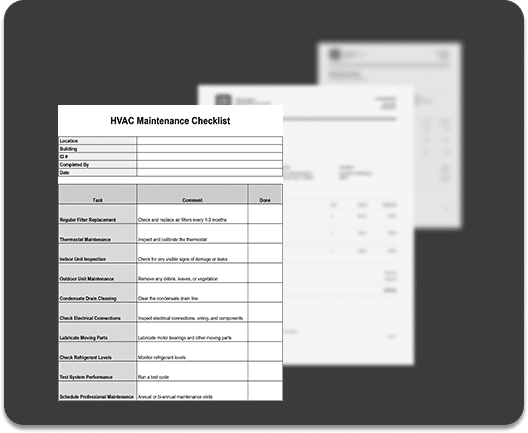
Data loss prevention (DLP) is a crucial aspect of any organization’s security and compliance strategy. DLP helps you protect your sensitive data from unauthorized access, leakage, or misuse. But how do you plan and implement DLP in a way that meets your specific needs and goals? In this blog post, we’ll introduce the three main steps of the planning process and the common elements that are involved in each step.
The first step is to identify the stakeholders who can provide input and guidance on the data protection requirements, risks, and priorities for your organization. These stakeholders may include regulatory and compliance officers, legal officers, security and compliance officers, agency leaders, agency workers, and IT staff. The second step is to describe the categories of sensitive information that you need to protect and the organizational processes that use them. For example, you may need to protect financial, medical, privacy, or custom data categories. The third step is to set your protection goals and strategy and develop a plan that covers the discovery, policy development, testing, training, tuning, and review phases of your DLP deployment. By following these steps, you can ensure that your DLP approach is aligned with your organization’s needs and goals. For more information on getting started on your government’s DLP approach learn more at Learn DLP and Microsoft Security adoption.
Deploy a comprehensive security portfolio to optimize your security and resources.
Once you’ve developed your internal security assessment team, an important next step is to identify and map out all your organization’s applications and data connections (internal or third party) that could be compromised in an attack. Assessing all attack vectors is critical in multi-cloud environments as it is how successful phishing attempts scale quickly through an organization. Overcoming the siloed approach in a multi-cloud environment can be a challenge. We also know that detecting, responding, and successfully remediating these attacks is a slow process, involving different security groups, and requiring different tools. It requires significant orchestration to ensure each of these point solutions are working together to ensure nothing slips through the cracks. Once the assessment and analysis are complete a detailed report outlining costs, time of work, and organizational need can help your leadership determine a long-term optimized security strategy that can help maximize your security investments, and reduce threat vectors.
Another trend that is reshaping the IT landscape is vendor rationalization. This is the process of consolidating and simplifying your vendor portfolio to reduce costs, complexity, and redundancy. According to Enterprise Strategy Group research, over the past 24 months, organizations have rationalized vendors in security and IAM, collaboration, and productivity areas. The results have been impressive: more than 9 out of 10 organizations reported improved end-user experience, eliminated redundant solutions, and increased IT efficiency. The return on investment on vendor rationalization has been very positive for most organizations, especially in security and identity and access management solutions. And if you are wondering how Microsoft 365 Government fits into this picture, the answer is simple: organizations with higher Microsoft 365 adoption are more confident in their ability to adapt and thrive through disruptions. Also, Microsoft 365 Government and Microsoft Azure Government are purpose-built with Zero Trust as a core architectural principle. And with comprehensive, integrated solutions for information protection, data governance, risk management, and compliance, Microsoft Purview builds on all four pillars to help protect your organization.
In this blog we’ve shared just a few of many actions your organization can take to start reviewing and building your IT security resiliency with Microsoft 365 Government. For more information check out the adoption resources and stay connected to the conversation in our Public Sector and Security, Compliance, and Identity Communities.